Cyber
BBN drives advancements in full-spectrum cyberspace operations for the Department of War and intelligence community customers. BBN develops and deploys multi-domain cybersecurity solutions through secure software development, cyber-physical systems research, high-fidelity network modeling and simulation, reverse engineering, and vulnerability analysis, offering critical insights into emerging threats and ensuring robust protection for complex systems. Researchers use operational expertise to deliver autonomous and semi-autonomous approaches to exploit and defend the three layers of cyberspace – physical, logical and social-cognitive. To deliver full-spectrum cybersecurity, BBN’s efforts focus on resilient architectures and enabling techniques, adaptive cyber defense, cybersecurity analytics, and cyber-physical and cross-domain system security.
Resilient architectures and enabling techniques
BBN delivers secure, uninterrupted system performance by developing architectures that actively detect, contain and recover from cyberattacks. As software systems grow in complexity and scale, the risk of disruption increases across critical domains. BBN improves system integrity and operational continuity by applying design principles such as isolation, state management and continuous monitoring, along with advanced techniques tailored for complex software environments. These techniques are designed to block escalation pathways, preventing attacks from spreading and minimizing their impact on mission-critical operations.
Showcase Program
DARPA’s Compartmentalization and Privilege Management (CPM)
Challenge
Solution
Benefit
This material is based upon work supported by the United States Air Force and DARPA under contract number FA8750-23-C-B031. Any opinions, findings, and conclusions or recommendations expressed in this material are those of the author and do not reflect the views of the United States Air Force and DARPA.
Adaptive cyber defense
To strengthen cyber defenses against increasingly automated and sophisticated threats, BBN develops adaptive strategies that accelerate threat detection, enable timely, effective responses and maintain coordinated control across the entire system. These strategies combine multiple layers of defense, incorporating traditional security controls, AI and machine learning to interpret threat information at different timescales and deception methods designed to expose adversaries. This layered approach delivers the speed, accuracy and adaptability needed to defend against evolving cyberthreats.
Showcase Program
DARPA’s Verified Security and Performance Enhancement of Large Legacy Software
(V-SPELLS)
Program goal
Challenge
Solution
Benefit
Distribution Statement “A” (Approved for Public Release, Distribution Unlimited).
Cybersecurity analytics
BBN improves system assurances and cyber resilience through advanced analytics that uncover critical vulnerabilities and provide actionable insights into software and network behavior. These insights are generated by applying methods such as program analysis to examine software structure, reverse engineering to understand both known and unknown code and systems, network analysis to detect abnormal activity and modeling to analyze system behavior and logic. To complement these methods, BBN uses red teaming to further validate system defenses by replicating real-world attack scenarios, testing defenses under realistic conditions and revealing potential exploitation paths. Together, these approaches accelerate risk identification and enable faster, more informed responses to emerging threats.
Showcase Program
DARPA’s Intelligent Generation of Tools and Security (INGOTS)
Program goal
Challenge
Solution
Benefit
Distribution Statement “A” (Approved for Public Release, Distribution Unlimited).
Cyber-physical and cross-domain system security
BBN secures complex systems that span cyber-physical, tactical, enterprise and warfighting domains, where interactions across boundaries often introduce hidden vulnerabilities. These domain crossings, critical seams where data and control shift between environments, can become attack surfaces if left unprotected. BBN reduces this risk by designing monitored and constrained crossings, paired with adaptive interface controls that manage information flow and maintain security integrity. This approach ensures reliable, secure integration across diverse, multi-domain systems and lays the groundwork for the intelligent, autonomous deployment of cross-domain applications in the future.
Latest BBN news

RTX's BBN Technologies unveils auto-switching system that keeps critical data alive
PACE4ACE automatically reroutes network traffic in contested environments to ensure uninterrupted communications

RTX's BBN Technologies launches open-source tool to validate covert cyber networks
DARPA-funded Maude-HCS rapidly validates hidden communications

DARPA taps RTX to advance kilometer-range X-ray vision
RTX BBN Technologies to develop long-range X-ray imaging algorithms to enable the identification of hard-to-access objects
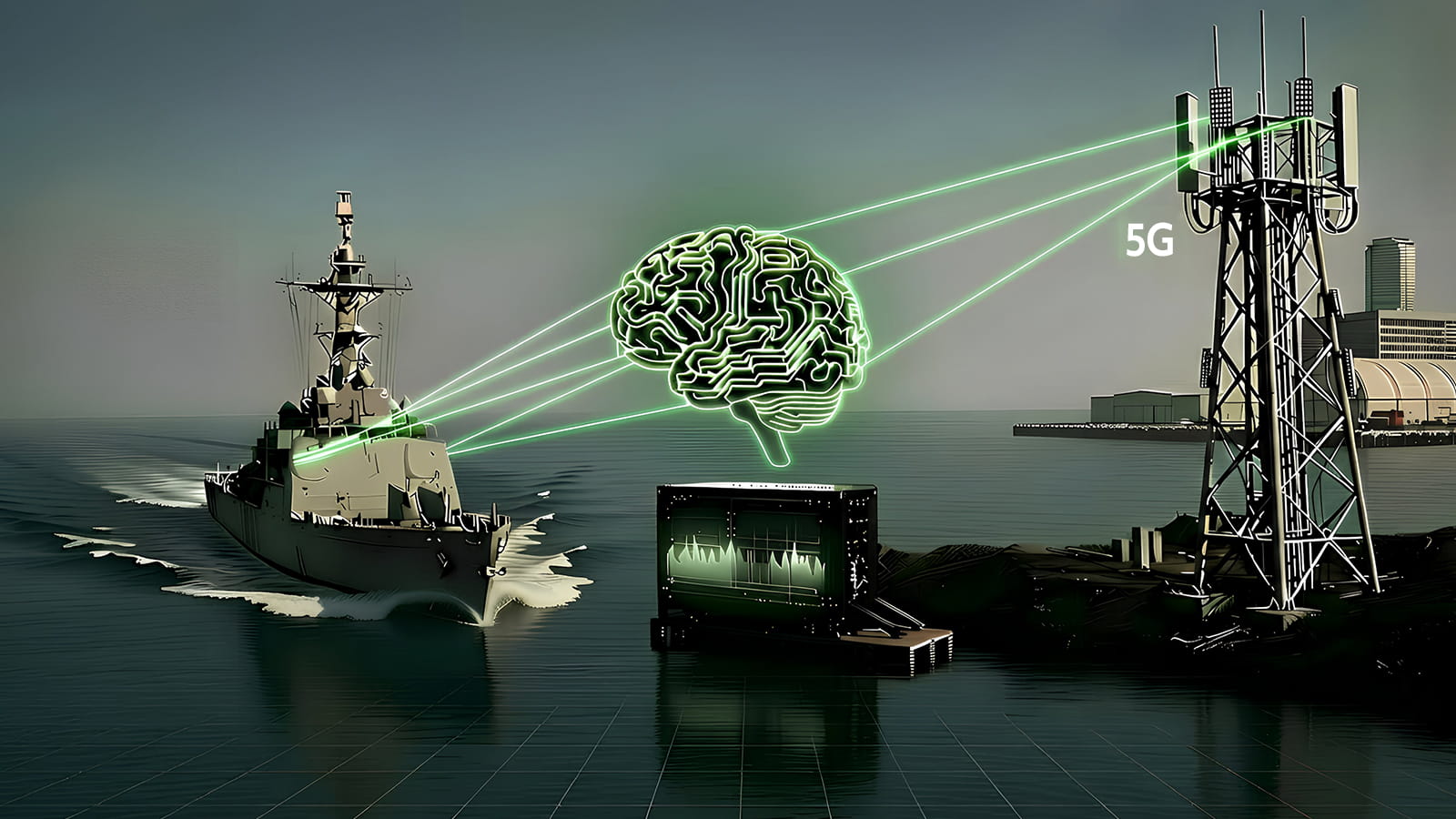
RTX BBN Technologies leads multi-team effort to demonstrate secure, real-time spectrum coexistence for 5G, defense radar
Team to build prototype that protects defense radars when the 3.1 to 3.45 GHz band is opened for commercial use



